In the rapidly evolving world of technology, remote SSH access for IoT devices has become an essential skill for developers, hobbyists, and tech enthusiasts alike. As more devices become interconnected, the ability to manage and configure them remotely is no longer a luxury but a necessity. Whether you're working on a home automation project or building a large-scale IoT network, understanding how to set up free remote SSH access can save you time, effort, and money.
This article will explore the concept of remote SSH access for IoT devices, focusing on free and efficient methods to achieve secure connectivity. We'll cover everything from the basics of SSH to advanced configurations, ensuring you have a comprehensive understanding of the topic. By the end of this guide, you'll be equipped with the knowledge to implement remote SSH access for your IoT projects without breaking the bank.
As technology continues to advance, the demand for secure and reliable remote access solutions grows. With the increasing number of IoT devices in use, it's crucial to understand how to manage them efficiently. This guide will provide you with the tools and techniques needed to establish remote SSH access, ensuring your IoT devices remain secure and accessible from anywhere in the world.
Table of Contents
Introduction to Remote SSH Access for IoT Devices
Why Is Remote SSH Access Important for IoT?
Setting Up SSH on Your IoT Device
Enabling Remote Access with SSH
Using Free Tools for Remote SSH Access
Troubleshooting Common SSH Issues
Best Practices for Remote SSH Access
Real-World Applications of Remote SSH Access
Introduction to Remote SSH Access for IoT Devices
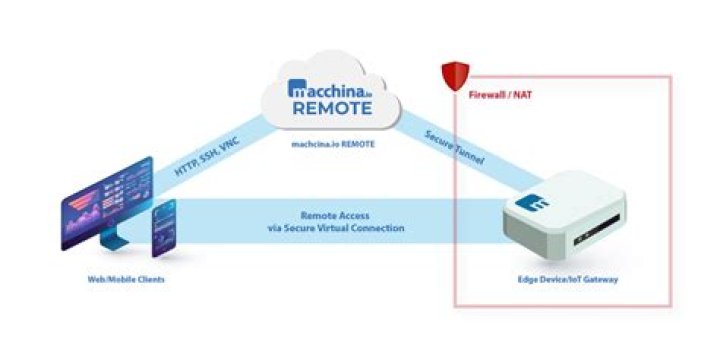
Remote SSH access is a fundamental tool for managing IoT devices from a distance. SSH, or Secure Shell, is a network protocol that allows users to securely connect to remote devices over an unsecured network. When it comes to IoT, this capability is invaluable, enabling administrators to monitor and control devices without physical access.
What is SSH?
SSH is a cryptographic protocol that provides a secure channel over an insecure network. It is widely used for remote command-line login and other secure network services. For IoT devices, SSH offers a reliable method for executing commands, transferring files, and managing configurations remotely.
Why Choose SSH for IoT?
SSH is preferred for IoT applications due to its robust security features and ease of use. It encrypts all data transmitted between the client and server, ensuring confidentiality and integrity. Additionally, SSH supports authentication methods such as passwords and public-key cryptography, adding an extra layer of security to your IoT setup.
Why Is Remote SSH Access Important for IoT?
Remote SSH access plays a critical role in the management and maintenance of IoT devices. As these devices are often deployed in remote locations, having the ability to connect to them securely is essential for troubleshooting, updating firmware, and monitoring performance.
Enhanced Security
With SSH, you can ensure that all communications between your IoT devices and your workstation are encrypted, protecting sensitive data from potential threats. This level of security is crucial, especially when dealing with devices that handle personal or confidential information.
Cost-Effective Solution
Implementing remote SSH access for IoT devices is a cost-effective solution compared to proprietary remote access solutions. By leveraging free and open-source tools, you can achieve secure connectivity without incurring additional expenses.
Setting Up SSH on Your IoT Device
Before you can establish remote SSH access, you need to set up SSH on your IoT device. This process typically involves enabling the SSH service and configuring basic settings to ensure secure communication.
Enabling SSH on Popular IoT Platforms
- Raspberry Pi: SSH is enabled by default on most Raspberry Pi operating systems. However, if it's disabled, you can enable it through the Raspberry Pi Configuration tool or by editing the SSH configuration file.
- Arduino: While Arduino devices don't natively support SSH, you can use additional modules like the ESP8266 or ESP32 to enable SSH functionality.
- Other IoT Devices: For other platforms, check the manufacturer's documentation for specific instructions on enabling SSH.
Enabling Remote Access with SSH
Once SSH is set up on your IoT device, the next step is to enable remote access. This typically involves configuring your router and firewall to allow incoming SSH connections.
Port Forwarding
To enable remote access, you'll need to configure port forwarding on your router. This process involves directing incoming SSH connections (usually on port 22) to the IP address of your IoT device.
Dynamic DNS
If your IoT device is behind a dynamic IP address, consider using a Dynamic DNS (DDNS) service. This will allow you to access your device using a consistent domain name, even if your IP address changes.
Securing Your SSH Connection
Security is paramount when it comes to remote SSH access. Implementing best practices can help protect your IoT devices from unauthorized access and potential attacks.
Use Strong Passwords
Ensure that all SSH accounts have strong, unique passwords. Avoid using easily guessable passwords or default credentials provided by the manufacturer.
Implement Public-Key Authentication
Public-key authentication is a more secure alternative to password-based authentication. It involves generating a pair of cryptographic keys and using them to authenticate SSH sessions.
Using Free Tools for Remote SSH Access
Several free tools are available to facilitate remote SSH access for IoT devices. These tools can simplify the setup process and enhance the security of your connections.
SSH Clients
- PuTTY: A popular SSH client for Windows users, offering a simple interface for connecting to remote devices.
- OpenSSH: A widely used SSH client and server suite available on most Unix-based systems.
SSH Servers
- Dropbear: A lightweight SSH server suitable for resource-constrained IoT devices.
- OpenSSH Server: The standard SSH server implementation, known for its reliability and security features.
Troubleshooting Common SSH Issues
Even with careful setup, issues can arise when configuring remote SSH access. Below are some common problems and their solutions:
Connection Refused
If you receive a "Connection refused" error, ensure that the SSH service is running on your IoT device and that your router is correctly configured to allow incoming connections.
Authentication Failed
Authentication failures can occur due to incorrect passwords or mismatched keys. Double-check your credentials and ensure that your public key is correctly installed on the server.
Best Practices for Remote SSH Access
Following best practices can help you maintain a secure and reliable remote SSH setup for your IoT devices.
Regularly Update Firmware
Keep your IoT device firmware up to date to protect against known vulnerabilities and ensure optimal performance.
Monitor Logs
Regularly review SSH logs to detect and respond to suspicious activity. This proactive approach can help prevent unauthorized access and potential security breaches.
Real-World Applications of Remote SSH Access
Remote SSH access has numerous applications in the IoT space, ranging from home automation to industrial monitoring. Below are some examples of how this technology is being used in real-world scenarios:
Smart Home Automation
Remote SSH access allows homeowners to manage their smart home devices from anywhere, ensuring convenience and peace of mind.
Industrial IoT
In industrial settings, SSH is used to monitor and control critical infrastructure, enabling real-time decision-making and reducing downtime.
Conclusion and Next Steps
Remote SSH access for IoT devices is a powerful tool that offers numerous benefits, including enhanced security, cost savings, and increased efficiency. By following the steps outlined in this guide, you can set up and secure remote SSH access for your IoT projects without the need for expensive proprietary solutions.
We encourage you to experiment with the techniques discussed in this article and explore additional resources to deepen your understanding of SSH and IoT. Feel free to leave a comment below if you have any questions or would like to share your experiences with remote SSH access. Additionally, don't forget to explore other articles on our site for more insightful content related to IoT and technology.
Sources:
- https://www.ssh.com/
- https://www.raspberrypi.org/documentation/remote-access/ssh/
- https://www.openssh.com/